System Architecture
How Sentinel fits into your environment.
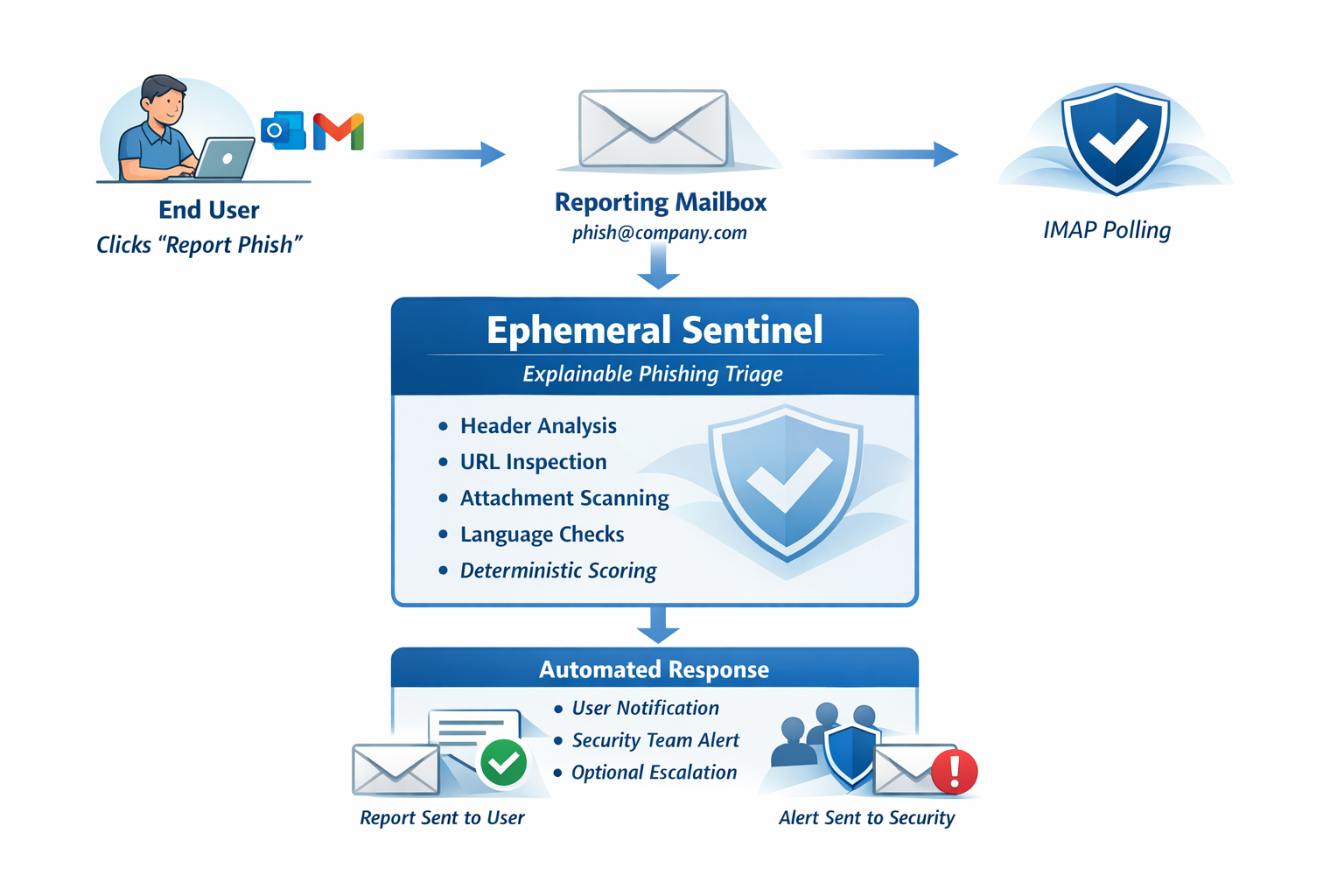
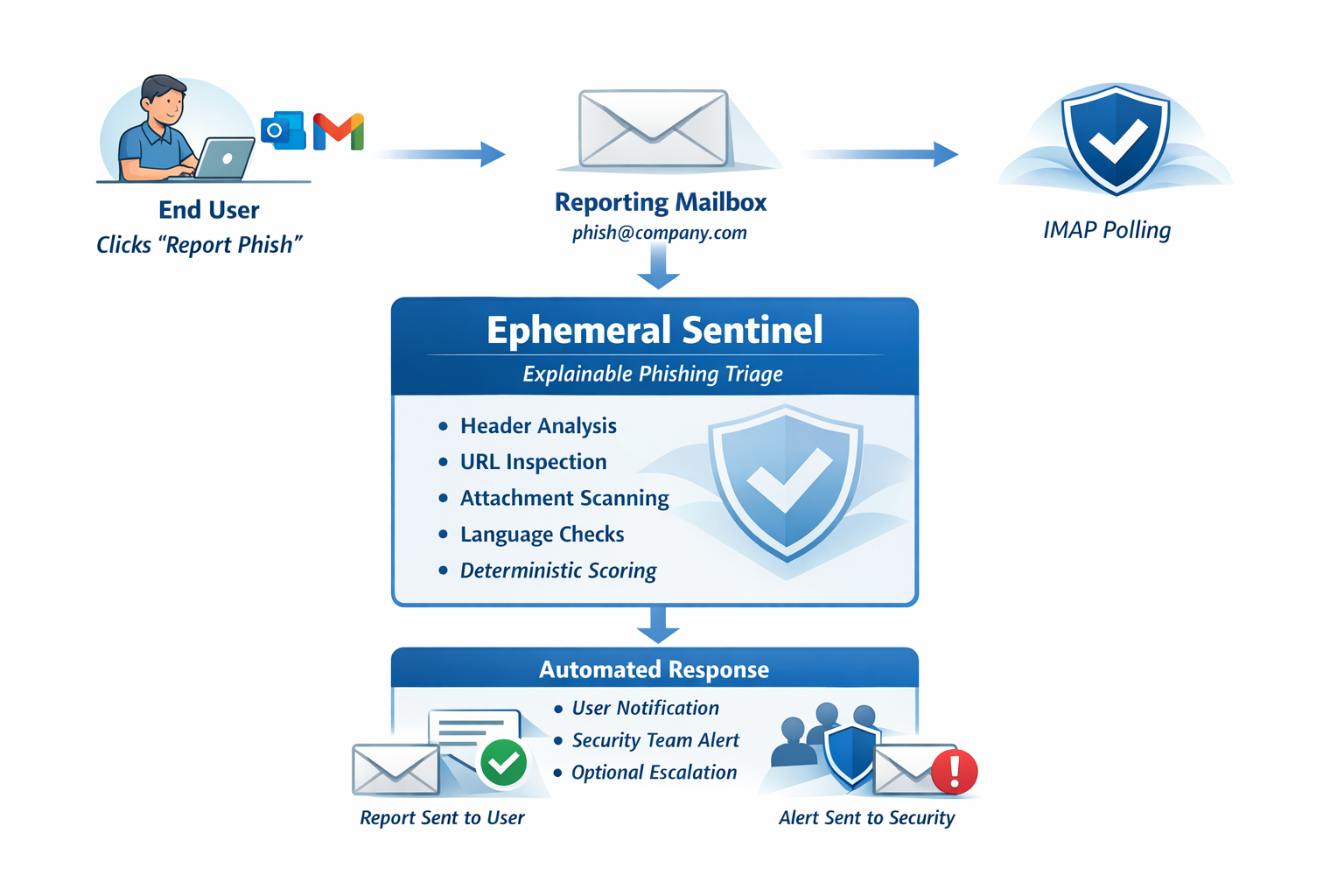
The diagram below shows the complete flow from a user reporting a suspicious email to the structured analysis being returned.
Architecture
Ephemeral Sentinel integrates with infrastructure you already have. No changes to mail flow. No inbound ports. No new risk.
System Architecture
The diagram below shows the complete flow from a user reporting a suspicious email to the structured analysis being returned.
Workflow
Every phishing report follows the same path — from the employee's inbox to a structured analysis returned in seconds.
.eml file.
phishing@yourdomain.com.
This is a standard mailbox that already exists in most environments using
a phishing report button. No new mailbox infrastructure required.
.eml is parsed and loaded into memory.
The deterministic analysis engine evaluates: email headers and routing path,
SPF / DKIM / DMARC authentication results, sender domain characteristics,
phishing language indicators, embedded URLs, and attachment file types.
All analysis is local — no content leaves the environment.
Design Principles
Ephemeral Sentinel was designed to be a low-risk addition to any environment. These principles guided every architectural choice.
Technical Details
Sentinel is designed to be lightweight and easy to understand. No complex dependencies. No black boxes.
| Component | Details |
|---|---|
| Deployment | Docker container. Runs on any container-capable host. |
| Mailbox Connectivity | Outbound IMAP (port 993 / TLS). Compatible with M365, Google Workspace, self-hosted. |
| Inbound Ports | None required. |
| Analysis Engine | Deterministic rule-based. No ML model. No AI API. |
| Email Retention | None. Email content processed in memory and discarded. |
| Persistence | SQLite — report metadata only (timestamp, risk score, signal list). No email content. |
| External Calls | None. All analysis is local. |
| Report Delivery | Email reply to reporting user. Optional CC to security team address. |
| Analysis Coverage | Headers, SPF/DKIM/DMARC, domain signals, language patterns, URLs, attachments. |
| Risk Output | Benign / Suspicious / Malicious — with weighted signal scoring. |
Analysis Engine
Eight analysis modules run against every reported email. Each contributes to the final risk score and report.
Next Steps
Review the example report to see a complete Sentinel analysis, or explore the pages tailored to your specific context.
Ephemeral Sentinel is available for pilot deployments with MSPs and organizations that want to improve phishing reporting workflows.
Discuss a Pilot