Ephemeral Sentinel
Explainable phishing analysis for every email your users report. Automated. Deterministic. No analyst required.

Explainable phishing analysis for every email your users report. Automated. Deterministic. No analyst required.

The Problem
Organizations invest in phishing reporting tools. Users are encouraged to click Report Phish when they receive something suspicious. Dedicated mailboxes get set up. Training materials remind employees why reporting matters.
Then the reports pile up. Security teams don't have time to review every forwarded email. Users hear nothing back. After a few experiences with silence, they stop reporting entirely.
The feedback loop breaks. Security awareness degrades. Threats go unexamined.
The Solution
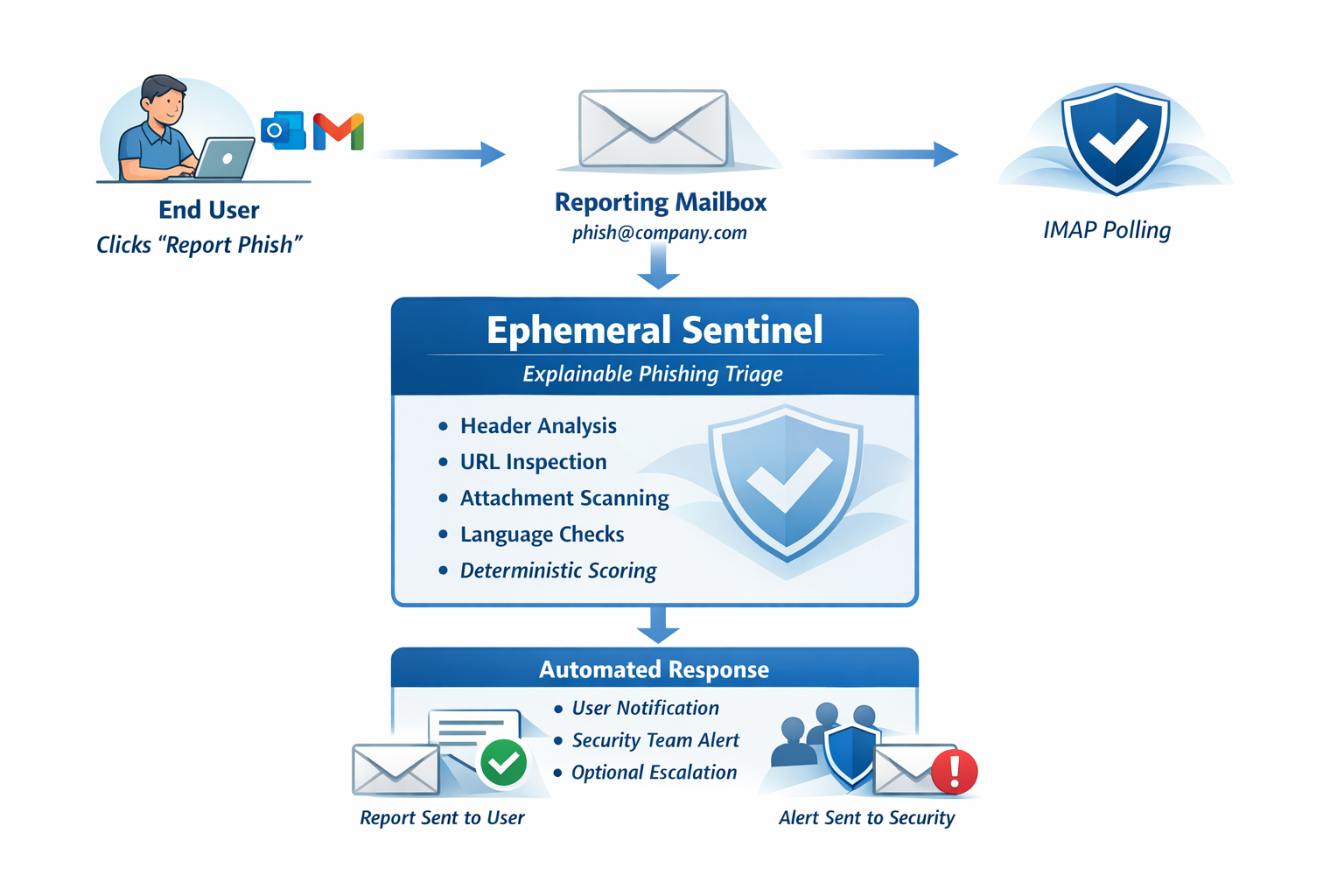
Ephemeral Sentinel automatically analyzes reported phishing emails the moment they arrive. No analyst required. No waiting. No silence.
How It Works
Sentinel connects to the reporting mailbox your Report Phish button already forwards to. Nothing else changes.
Who It's For
Ephemeral Sentinel serves two primary audiences with different goals but the same need: automated, explainable phishing analysis.
Deploy Sentinel inside each client environment. Every reported email receives automated analysis. Your analysts focus on real threats, not manual triage.
Every phishing report becomes a learning moment. Employees receive plain-language explanations. Security teams receive structured triage automatically.
Security Design
Every architectural decision in Ephemeral Sentinel was made to minimize operational risk, attack surface, and data exposure.
Example Output
Every analysis returns a structured report explaining what was found, in plain language that doesn't require a security background to understand.
About
Ephemeral Sentinel was created by a security and infrastructure practitioner with decades of experience in operational environments — environments where phishing reports accumulate in unattended mailboxes, analysts are stretched too thin for manual triage, and the feedback loop between reporting users and security teams never closes.
The tool exists because the problem is structural, not motivational. Organizations don't fail to respond to phishing reports because they don't care — they fail because manual review at scale doesn't work. Sentinel was designed to remove that constraint.
It was built to be the kind of tool a practitioner would actually want deployed: no external dependencies, no data retention, no inline risk, no AI black box. Deterministic analysis, delivered automatically, to the people who need it.
Get Started
Review the architecture to understand how Sentinel fits your environment, or explore the example report to see what your users would receive.
Ephemeral Sentinel is available for pilot deployments with MSPs and organizations that want to improve phishing reporting workflows.
Discuss a Pilot